Intelligence gathering is the first line of defense against terrorism. Through use of intelligence, law enforcement and military operations can be designed to disrupt terrorist organizations and preempt their operations. Prior to September 11, 2001, most state and local law enforcement agencies viewed intelligence gathering on global terrorist groups as the purview of the federal government. Except for large cities like Los Angeles and New York, if state or local agencies gathered intelligence it tended to be on domestic subversive groups. We have since realized that some terrorist organizations have a global reach, and that state and local law enforcement officials must broaden their view.
While it is not likely that your agency will send someone to participate in an intelligence operation against the Manuel Rodriguez Patriotic Front in Chile or the Revolutionary Nuclei in Greece, it is likely that you will read and act upon distilled intelligence. In other words, you are very likely to receive an intelligence report that gives you information and there is an expectation that you act. By knowing some of the methods by which terrorists organize and communicate, you may be in a better position to judge that information and plan for your community. Moreover, while our focus is on international terrorist organizations, there are many domestic groups that use similar methods of organizing and communicating. Understanding some of their organization and communication methods may help you see evidence, information and intelligence you might have otherwise overlooked.
Single Celled Organisms
Terrorist organizations are often described and constructed using the biological analogy of a cell. Biologically, a cell is the basic unit of life. While most of the organisms with which we are familiar are multi-cell units, there are many single cell organisms. In the realm of terrorism, the single celled organism is referred to as the Lone Wolf terrorist or leaderless resistance. This can be a critical concept in understanding the development of terrorist organizations. The Lone Wolf terrorist does not receive direct instructions from a central organization. Rather, he or she receive inspiration from an idea or perhaps a remote subversive political figure.
Domestically, Lone Wolf terrorists have included Timothy McViegh (Oklahoma City Bomber), Eric Rudolph (Olympic Park Bomber) and Buford Furrow (firearm attack on a Jewish Daycare center in Los Angeles and murder of a Postal Carrier). Internationally, there is strong evidence to suggest that some terrorist acts attributed to Al Qaeda were not committed by the group so much as inspired by the group. Furthermore, domestic terrorist groups such as the Earth Liberation Front (ELF) are probably best categorized as leaderless resistance rather than a cellular organization. This means that small cells or individual terrorists are motivated by the groups overarching goals but not coordinated by nor in direct communication with the larger group itself.
Single celled or disconnected cellular groups have the benefit of maximum operational security because communication is limited or non-existent. There are few, if any, opportunities for an intelligence service to intercept communications or penetrate the group. On the other hand, single celled or disconnected cellular groups are also limited in their ability to carry out operations. While McViegh, Rudolf and Furrow were able to commit horrendous acts of terrorism, their status as Lone Wolves meant they left a long trail of evidence because they had to make all purchases, conduct all reconnaissance, prepare all the equipment and conduct the operation. Like any mass murder or serial killer, these terrorists did not have the benefit of cellular specialization to mask their trail. Moreover, Lone Wolves are limited in their ability to sustain long-term terrorist campaigns because the evidence they leave will ultimately lead to their arrest. It takes a much more complex organization to continue terrorist operations over the long-term. In the instance of Lone Wolves, state and local law enforcement officials should be aware of purchase of certain materials, suspicious actions of individuals and devise ways to share seemingly low-level suspicious activities with other jurisdictions.
Multi-celled organisms
As biological organizations become more complex, their cells tend to specialize. As an example, we have nerve cells, muscle cells and bone cells. Each of these cells has developed a particular specialization so that the larger organism can be more efficient. However, for these specialized cells to work together in the larger organism they must communicate. With terrorist organizations, the purpose of a true cellular organization is to increase the operational security of the larger group and to capitalize on specialization.
It is a mistake to believe that one member of the cell necessarily leads to other cells. Rather, operational security is enhanced because most of the members of the cell do not know anyone in the organization outside of the cell. This lack of knowledge of the larger organization is like the cellular membrane that defines and protects the cell. If the cell is compromised through member arrest or intelligence penetration, only the cell is damaged and not the larger organization. . For maximum operational security there may be only blind communication between cells. In other words, the leader of the cell may simply receive instructions through some blind form of communications and not in any face to face meeting.
In cellular terrorist organizations there tend to be two types of cells operational and support. An operational cell is a self-contained, often single mission entity designed to carry out an operation and then likely be killed or captured. The 9/11 terrorist were a single-mission operational cell.
Many terrorist organizations also have support cells. These cells are designed to support long-term, sustained, terrorist operations. A homicide bomber who is part of a larger, sustained terror campaign can be supported by many types of support cells. For a homicide bomber there could be a recruitment cell, minder cell, reconnaissance cell, bomb-making cell and a delivery cell. Additionally, there are likely planning and coordination cells assisting the other supportive cells. Sustained terror campaigns like those conducted in the Middle East require this type of specialization. Consider that bomb makers are a terrorist resource that is not easy to replace. Because they are so difficult to replace, the bomb maker is often insulated from operations in their own, tightly control support cell. Bomb makers rarely deliver or detonate their own devices. They dont recruit the bomber, survey the target nor take on the role of a minder (the person(s) who monitor the bomber between the period of recruitment and employment). Bomb makers may not even procure their own components.
Complexity and Chatter
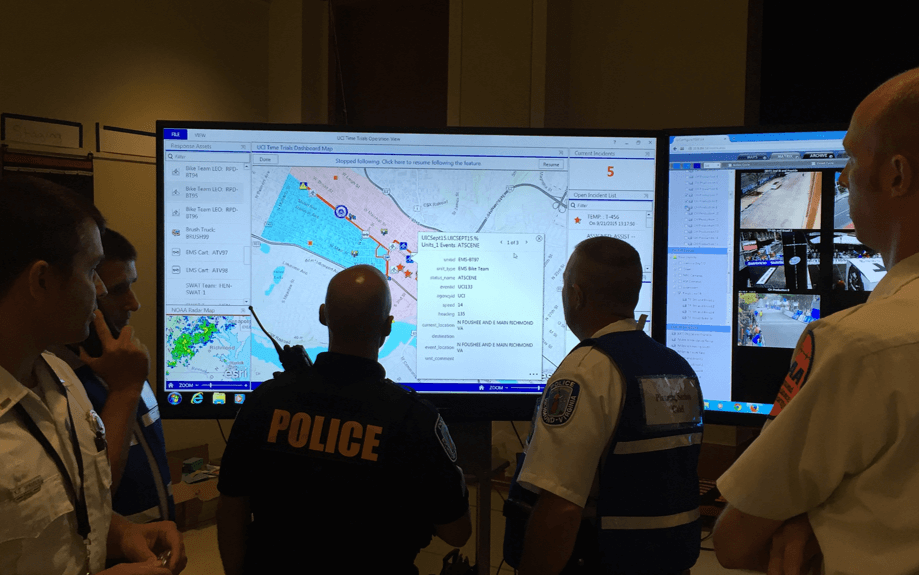
As a terrorist organization becomes more specialized and cellular, its communications scheme becomes more complex. Think about a law enforcement operation that was planned in advance. Perhaps a major convention was coming to your community. Six months prior to the event there were telephone calls, memos and meetings to begin the planning process. As the convention neared, the communications between participants likely increased in their frequency and intensity. Then, the communication likely peaked the day or so before and operational communications began. There was a natural build-up, peak and then operational drop in communications.
Intelligence reports that speak of an increase in chatter are reflecting the same build-up, peak and then drop. In the intelligence world this is referred to as signals intelligence or SIGNIT. Because of the natural cycle of pre-operational communications, SIGNIT does not necessarily have to understand the signals. As a predictor, SIGNIT doesnt necessarily have to know what is being said; only that a predictable pattern of communications is increasing. Moreover, because the location of likely command and control, support, and operational cells is known or can be presumed, the increasing cycle and the flow of communications between geographic regions provides additional evidence that a terrorist operation is likely.
They Know What We Know
Like many complex, multi-cell organisms, terrorist organizations are learning organizations. Indeed, to survive over the long-term they must adapt their methods and there is some evidence to suggest that they modify their message as they age and change. As learning organizations, they know about the predictive value of chatter and are likely developing new methods of communication that reduces the raw SIGNIT value. One way to reduce the susceptibility of their communications to interception and interpretation is to disguise their communications.
In the last few years there has been talk about the use of Stenography as a means of disguising communications. Stenography is the hiding of a message, particularly an image, within another message or image. In the digital world a photograph is transmitted by reducing it to a computer code. You have seen this computer code files of photographs JPEG, GIF, etc. At its simplest, inside those files there is room to insert other lines of code which could contain a message. However, to-date, there have been no public reports of terrorists using this technique.
The terrorists are well-aware of the United States capability to intercept cellular telephone traffic. In addition to reducing their use of this mode of communications, they are likely taking advantage of pre-paid cellular telephones. This allows greater anonymity and the flexibility to change cellular numbers and service providers easily. While there have been no confirmed reports of terrorist using pre-paid cellular, there is significant information to suggest that other criminal organizations, like gangs and narcotics traffickers are taking advantage of this technology. Law enforcement officials should be sensitive to any reports of suspicious or large purchases of pre-paid cellular telephones.
An interesting place to see how terrorists are using the Internet is the Search for International Terrorist Entities, or the SITE Institute. This organization monitors terrorist websites and communications.
The Internet has provided global and instantaneous communications. There has been quite a bit of news about how the government can monitor Internet communications. If you sent an email with certain key words you could expect the message to be flagged for human review. Indeed, it is very likely that if you sent an email from certain geographic regions, through certain Internet Service Providers and it contained certain key words it would be monitored.
Terrorists have tried to mask or disguise their use of email by having relatively anonymous accounts provided free by various services. But, any message you send over the email account is susceptible to interception. Terrorists devised a way to minimize decection by using anonymous email accounts not for transmission, but as holding files. As an example, Terrorist A wants to send a message to Terrorist Cell B. Terrorist A logs onto an email account, drafts a message and saves it as a draft. Terrorist Cell B is told through some other means that an email account will be established and the password. Terrorist Cell B periodically logs onto the same account and reads the drafts and changes them with a confirmation message. The draft is saved and never sent. This logging on and drafting prevents interception because the message is never sent. It remains one of millions of unsent messages.
While terrorist are using technology to communicate it is likely that they are mostly relying on time-tested spy tradecraft like dead drops. A dead drop is a pre-determined location where messages or material are left so that cell members do not have to meet face to face. Or, in areas where there is significant social support for their movements, face-to-face meetings. Whatever their means of communication, as the complexity of their cellular structure grows, so does the complexity of their communication schemes and the likelihood of interception. As learning organizations we can expect terrorist cellular groups to learn how law enforcement discovers them and then devise new means of covert, secure communications.